Data Security Concerns in Outsourcing Fintech Development
While outsourcing fintech software offers many benefits, such as cost-effectiveness and fast time-to-market, it also poses certain risks, particularly when it comes to data security and confidentiality. According to research, global cybercrime losses are expected to reach $10.5 trillion by 2025.
In this blog post, we will explore some best practices that will help ensure your data remains secure and confidential in the process of outsourcing development of your fintech software.
Data Security Concerns in Outsourcing Fintech Development
Since outsourcing fintech development involves dealing with a lot of sensitive financial data, keeping it secure is the number one challenge for you and your outsourcing partner.
Regular communication, monitoring, and collaboration with your outsourcing provider are musts for maintaining a strong security posture throughout the entire development process. Here are some key data security concerns when outsourcing fintech development.
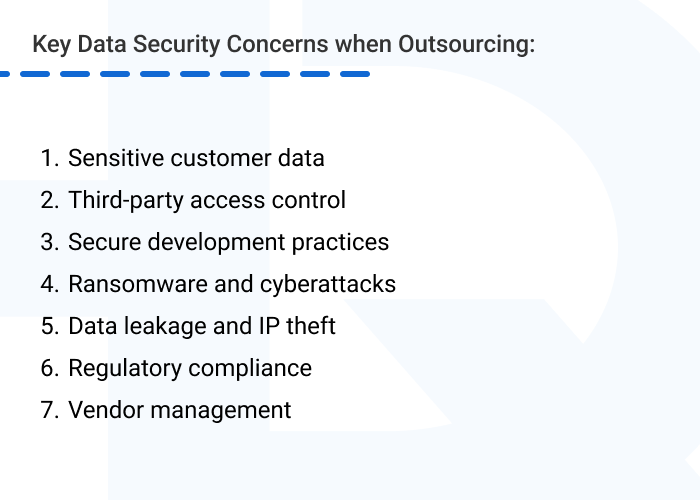
- Sensitive customer data. Financial technology apps and systems deal with sensitive customer data such as financial transactions, banking details, and personal information. Transferring this data to your outsourcing vendor increases security risks, as there is always a chance of data theft.
- Third-party access control. When outsourcing software development, you may need to grant access to sensitive financial data and current operational systems with important information.You need to establish strong access monitoring to restrict and audit this access.
- Secure development practices. To avoid data loss in case of a disaster or system failure, your outsourcing company must have a robust backup and recovery system.
- Ransomware and cyberattacks. Сybersecurity measures in place must protect against cyber threats such as hacking, phishing, malware, etc.
- Data leakage and IP theft. Even if you are confident that every piece of your data is secure, data leaking from your vendor’s side is always possible. To avoid it, assess the vendor’s security measures, protocols for protecting sensitive information and source code, and incident response plan in case of a breach.
- Regulatory compliance. Financial services have strict regulatory compliance requirements around data security and privacy such as GDPR (General Data Protection legislation), PCI DSS (the Payment Card Industry Data Security Standard), SOC 2 (Service Organization Control 2), etc. You must be sure that your outsourcing company complies with all relevant regulatory requirements to guarantee that the data is processed lawfully and securely.
- Vendor management. You should have a robust development plan to monitor IT outsourcing security practices and ensure compliance with contractual obligations.
Can’t choose an outsourcing vendor because of data security concerns?We at HQSoftware prioritize the security of your and your customers’ data. Let’s talk!
Anna Halias
Business Development Manager
Any weakness in your outsourcing vendor’s security could put your business data at risk. To avoid this, you should work proactively to keep your data safe.
How to Keep Outsourced Data Secure
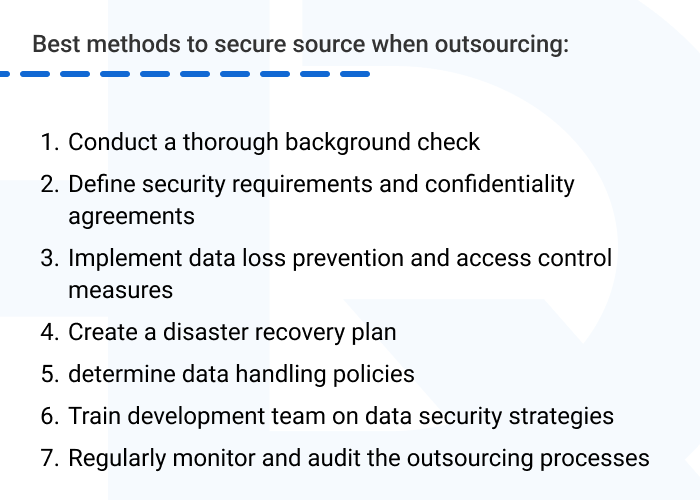
Unfortunately, you can’t unilaterally guarantee your outsourced data will be completely secure, as your software provider is equally responsible for its safety. That’s why it’s vital to thoroughly research potential outsourcing partners. Some of the best methods to be sure you can work securely with an outsourced developer include the following:
- conduct a thorough background check;
- define security requirements and confidentiality agreements;
- implement data loss prevention and access control measures;
- create a disaster recovery plan;
- determine data handling policies;
- train the development team on data security strategies; and
- regularly monitor and audit the outsourcing processes.
Conduct a thorough background check
Assessing the background of your potential vendor must be the first step before jumping into an outsourcing agreement. Anything that indicates legal and financial issues or a lack of integrity can be a red flag.
Examine your vendor’s security policies and practices, check references, and confirm that they adhere to all applicable laws and standards. Also, ensure that your outsourcing partner has sufficient security measures in place to protect against hacking and unauthorized access, such as encryption and multi-factor authentication tools.
It’s worth reviewing certifications such as GDPR, PCI DSS, and SOC 2 that can guarantee safeguarding of your sensitive information. This is important to ensure you won’t face legal disputes and potentially hefty fines down the road.
At HQSoftware, we always engineer financial software in compliance with legal requirements, to defend your business from cyber criminals and protect your company’s reputation. For example, one of our clients required HQSoftware to develop a tax management solution that would be in compliance with Swedish tax legislation. Since the solution is built to support all accounting activities, it automatically meets all requirements of the current tax legislation and provides tax reporting to the Swedish tax agency.
Determine data handling policies
Define clear data handling policies and procedures for the vendor to follow. This includes specifying how to handle, store, and process data, as well as who has access to it.
First of all, make an audit of all types of sensitive data that outsourced developers may access. This includes personal identifying information, financial info, intellectual property, etc. Then differentiate sensitive data based on potential harm from unauthorized access or disclosure. This helps determine appropriate security controls.
Define data retention periods and require outsourced developers to delete sensitive data once it is no longer needed for projects, restricting access to backups to authorized staff.
Define security requirements and confidentiality agreements
You should set up an outsourcing NDA (non-disclosure agreement) or a security agreement to guarantee that confidential information will not be shared with anyone unauthorized.
You will need to specify security expectations, obligations, audit rights, and penalties in legal contracts with your outsourced providers. It may also be important to address intellectual property rights and ownership issues.
Also, include in your security clauses a requirement that you must be notified immediately if any data security incidents or breaches occur involving your data.
You may require outsourced developers to comply with your organization’s security policies and procedures related to handling confidential information, if needed.
As your financial development software provider, we specify what confidential information can be used to ensure safety and confidentiality of your sensitive data.
Implement data loss prevention and access control measures
By implementing data loss prevention (DLP) solutions, you can monitor and prevent unauthorized transmission of sensitive data. This includes incorporating audit trails, logging data access, and reviewing access logs on a regular basis.
As an example, a financial solution that we developed for one of our clients makes it possible to collect data from a third-party service, aggregate it, remove any irrelevant data, and then stream real-time stock quotes to a secured page on the client’s website. Engineers at HQSoftware implemented the SSL protocol with required certificate authentication so as to attain an acceptable level of security.
With access controls, you can ensure that only authorized personnel have access to sensitive data. The best option here is to create a unique user account for each team member, implementing multi-factor authentication and restricting access to sensitive data on a need-to-know basis. To eliminate any issues, remember to grant developers the minimum access they need to complete their work and revoke access as soon as the work is done.
Another option to safeguard your sensitive information is to use data encryption. For instance, you may implement AES-256 (Advanced Encryption Standard), RSA (Rivest–Shamir–Adleman), and SHA-256 (Secure Hash Algorithm) to encrypt data both in transit and at rest. You can also isolate networks used by outsourced developers. Consider using virtual private networks (VPNs) with strict firewall rules..
Create a disaster recovery plan
To ensure that data can be recovered in the event of a data breach or other failure, you need a disaster recovery plan. This includes creating backups of critical data, testing recovery procedures, and creating a plan for notifying stakeholders in the event of a data breach.
Then ensure that backups of application code, configurations, data, and other artifacts are securely maintained in geographically separate locations if you work in different zones. Don’t forget to clearly communicate the disaster recovery plan and individual roles to the outsourced development team and provide training.
As your outsourcing provider, at HQSoftware, we create detailed, step-by-step instructions for recovering each critical application, including procedures for restoring from backups, rebuilding infrastructure, etc. We always determine the Recovery Time Objective (RTO) and Recovery Point Objective (RPO) for each critical system. This helps our development team to specify how quickly and to what point we need to recover data.
Train development team on data security strategies
For secure development you can guide outsourced developers through your specific processes, such as secrets management, code reviews, penetration testing, access controls, etc. It’s important to educate your outsourced developers on all relevant regulatory compliance requirements they must adhere to, related to secure development and data protection.
Regularly monitor and audit secure outsourcing processes
Beyond the initial check, consider periodic checks to identify any issues that arise over time. You may also retain the right to conduct security audits and reviews of the outsourced developers’ practices, systems, and facilities related to protection of confidential information. By routinely performing security assessments, penetration tests, and audits of the developing systems, you can ensure that the result meets expectations for quality, security, and compliance.
At HQSoftware, you can request audit reports and periodically review the security practices and controls used by your outsourcing providers. Proper KPIs, reviews, access controls, and testing uncover issues that can then be addressed, improving outcomes over time.
By following these practices, you can significantly reduce risks when outsourcing data and development activities. The key is to take a “defense-in-depth” approach, with multiple layers of security controls, monitoring, and oversight of outsourced developers.
Conclusion
By taking these steps, you can enjoy the benefits of outsourcing fintech development while maintaining the safety and security of your customers’ data. When outsourcing software development, it is important to stipulate the following security measures:
- conduct a comprehensive background check of your future outsourcing provider;
- determine data handling policies and conduct NDA outsourcing agreements;
- implement effective measures to prevent data loss;
- incorporate access control to sensitive data;
- create a disaster recovery plan and train the development team on data security strategies;
- regularly audit secure outsourcing processes.
Regular communication with your outsourcing partner and active involvement in the development process help ensure that data security concerns are addressed in a timely manner. At HQSoftware, we establish clear protection policies to develop secure first-rate financial software. In our 22 years on the market we’ve tackled both typical and specific security challenges in fintech projects, gaining strong expertise and proving ourselves as a reliable software development partner.
Please don’t hesitate to get in touch with us if you have any questions about our financial development services. We will schedule for you a free consultation and be happy to address any inquiries you may have.

Head of Production
To ensure the outstanding quality of HQSoftware’s solutions and services, I took the position of Head of Production and manager of the Quality Assurance department. Turn to me with any questions regarding our tech expertise.
Related Posts
View All
We are open to seeing your business needs and determining the best solution. Complete this form, and receive a free personalized proposal from your dedicated manager. Sergei Vardomatski Founder






